


14.09.2022
Cyberattacks are becoming increasingly organised and professional; almost every company in Germany has already been the victim of an attack, as a recent survey by bitkom shows. The consequences can be incalculable and in any case cause a forced disruption in business operations that hardly any company wants or can afford.
The attacks take place in different ways, so a comprehensive defence concept is indispensable to securely protect sensitive company data. For this reason, we present various measures in more detail here, which in combination represent an effective means against cyber attacks.
Firewall
The biggest gateway for viruses is still internet access. If this is not protected by special hardware in the form of a firewall, hackers have an easy game and gain easy access to your internal resources. A firewall shields your company network from the Internet by checking incoming and outgoing data traffic for malware and only allowing secure data into your own network.
In this area, we rely on the Firebox from our partner Watchguard. The WatchGuard Firebox is a comprehensive platform for network security. Thanks to universally applicable security and visualisation tools for threat detection, it offers complete control over your networks at enterprise level - regardless of the budget or complexity of the company. Different functions are available in customised security packages. In this way, the Firebox can be optimally adapted to the needs of your company, which we will be happy to analyse together with you.
IT security: Sensitised employees are the best protection
A popular gateway for criminals are the employees themselves. Attempts to manipulate access data to make it possible are carried out in a variety of ways. It is therefore all the more important to sensitise employees to these manipulations through training. Consequential damage from successful attacks often amounts to many times the investment in targeted employee training.
A combination of customised awareness training and phishing tests from our partner G DATA shows you in which sensitive areas your business data is particularly vulnerable to attack.
With the help of an e-learning platform, you raise the awareness of your colleagues and show them how to act securely at the same time: The various learning units can be prioritised individually according to knowledge level and played out to your employees in a targeted manner. The trainings combine descriptive tips, videos and multiple-choice questions on points that everyone in the office is confronted with almost every day: Can I click on the link? Can I open the document? Can I trust the person/website? The entertaining lessons are easy to integrate into daily work.
As part of the phishing tests, employees receive fake, but deceptively real-looking emails from a sender of a well-known company such as XING, Amazon, Outlook and similar.
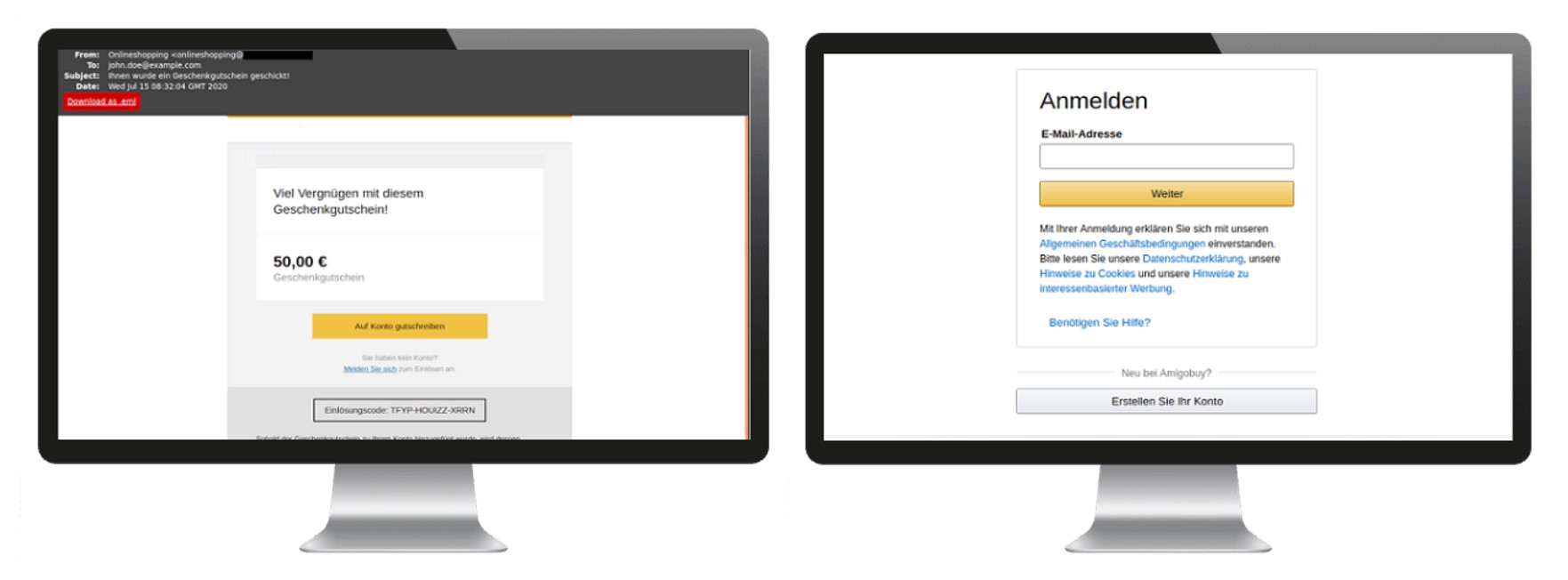
A total of 15 different campaigns can be selected here to suit individual needs. The aim of the e-mails is often to build up pressure on the employee and thus entice him or her to take an action in which, for example, he or she releases sensitive data such as access data or starts a download. It is precisely scenarios like these, which demand quick action by the employee and thus put him or her in a stressful situation, that hackers and cyber criminals trickily exploit time and again to gain access to your business data.
The test results of a planned phishing e-mail campaign show you in detail the success rate of the individual phishing attempts and display in categories which action the employee has carried out (open website, open e-mail, disclose sensitive data, open attachments, etc.). From this, targeted guidelines for dealing with e-mails can be created and training measures can be derived that can be individually implemented to protect your data.
High security thanks to two-factor authentication
At the same time, you can secure access to your data with two-factor authentication or multi-factor authentication. To secure logon processes and protect access to company resources, another factor can be added to this process in addition to the user name and password. This factor can be, for example, a code that you receive via SMS or an app on your smartphone.
Even if the personal password has been spied out by a third party, access is not possible without the mobile device or a token. As a concept, 2FA/MFA has proven itself and significantly improved the security of numerous accounts. So don't hesitate and let us check whether your company data is optimally protected.
Cyber Defence Status Check
Carry out a cyber defence status check together with our experts in just three steps, which will reveal possible weaknesses in your IT security concept.
Don't hesitate and let us check whether your company data is optimally protected. Do you have questions and need more information? Our experts are at your disposal, contact us directly.
TSO-DATA
Marvin Hitzfeld
it-infrastruktur[at]tso[dot]de
+49 (541) 1395-94