


13.12.2021
A critical vulnerability (Log4Shell) has been discovered in the widely used Java library Log4j. According to the assessment of the Federal Office for Information Security (BSI), this results in an extremely critical threat situation, because the affected library is very widespread and trivially exploitable. The first successful compromises have already been detected.
There is already a security update for the Java library, but in addition, the numerous products that use Log4j must also be adapted accordingly. The BSI's recommendation to companies is to implement the defensive measures outlined in the cyber security warning. In addition, detection and response capabilities should be increased in the short term in order to adequately monitor their own systems. Updates for individual products should be implemented immediately upon availability. Furthermore, examine all vulnerable systems for possible compromise.
We will be happy to support you in this process and answer your questions - please contact us directly.
In this context, also check your other security measures together with us, because according to the BSI, the threat situation from cyberattacks is growing rapidly.
A particularly popular gateway for criminals are the employees themselves. Attempts at manipulation to enable the release of access data can be carried out in many different ways. It is therefore all the more important to train employees to recognise these manipulations and thus to be able to maintain the protection of the company. Consequential damage from successful attacks often amounts to many times the investment in targeted employee training.
IT security: qualified employees are the best protection
It is extremely important to be able to rely on well-trained employees who recognise these dangers and act accordingly - for their own protection and that of the entire company.
Together with our partner G DATA, we offer customised awareness training as well as phishing tests that show you exactly in which sensitive areas your business data is particularly vulnerable. In this way, training measures can be coordinated in a targeted manner and used effectively.
With the help of an e-learning platform, you can raise your colleagues' awareness and show them how to act securely at the same time: The various learning units can be prioritised individually according to the level of knowledge and played out to your employees in a targeted manner. The trainings combine descriptive tips, videos and multiple-choice questions on points that everyone in the office is confronted with almost every day: Can I click on the link? Can I open the document? Can I trust the person/website? The entertaining lessons are easy to integrate into daily work.
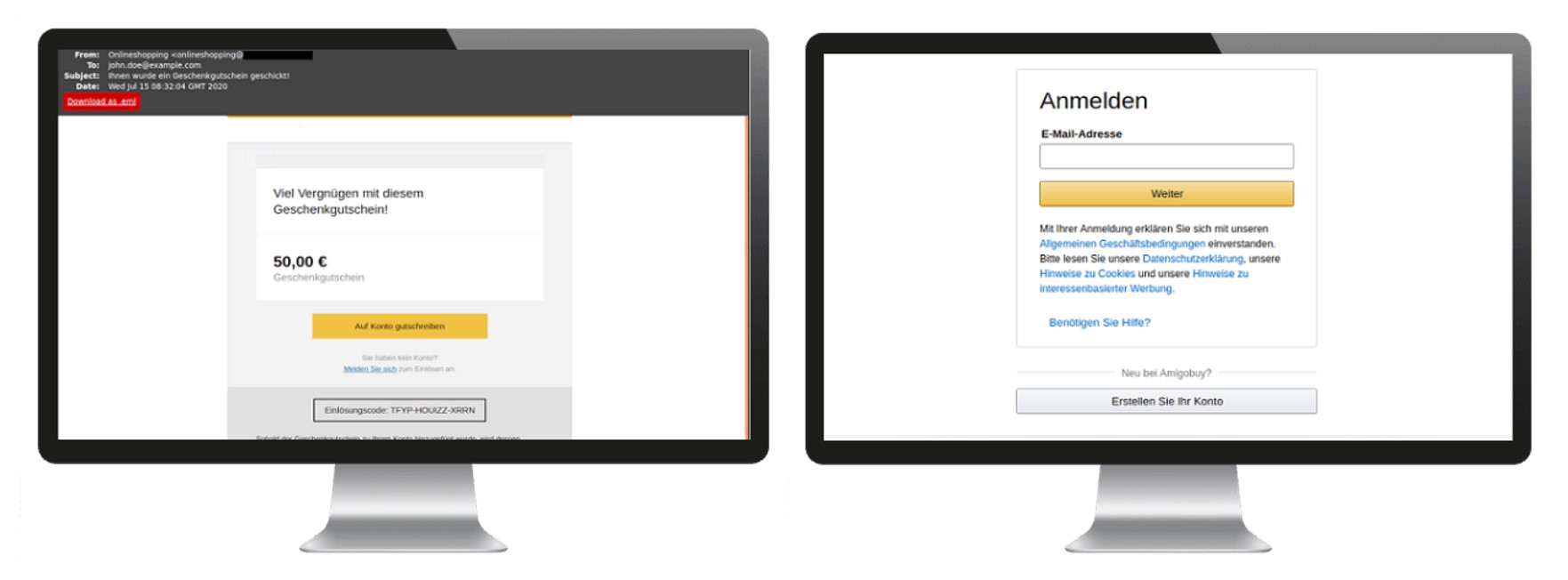
As part of the phishing tests, employees receive fake, but deceptively real-looking emails from a sender of a well-known company such as XING, Amazon, Outlook and similar.
A total of 15 different campaigns can be selected here to suit individual needs.
The aim of the e-mails is often to build up pressure on the employee and thus entice him or her to take an action in which, for example, he or she releases sensitive data such as access data or starts a download. It is precisely scenarios like these, which demand quick action by the employee and thus put him or her in a stressful situation, that hackers and cyber criminals trickily exploit time and again to gain access to your business data.
The test results of a planned phishing email campaign show you in detail the success rate of the individual phishing attempts and display in categories which action the employee has carried out (open website, open mail, disclose sensitive data, open attachments, etc.). From this, you can then create targeted guidelines for dealing with e-mails and also derive training measures that can be carried out individually to protect your data.
High security thanks to ZFA
At the same time, you can secure access to your data with two-factor authentication. To secure logon processes and protect access to company resources, another factor can be added to this process in addition to the user name and password. This factor can be, for example, a code that you receive via SMS or an app on your smartphone.
Even if the personal password has been spied out by a third party, access is not possible without the mobile device or a token. As a concept, 2FA/MFA has proven itself and significantly improved the security of numerous accounts. So don't hesitate and let us check whether your company data is optimally protected.
Do you have questions and need more information? Our experts are at your disposal, get in touch right away.
TSO-DATA
Marvin Hitzfeld
it-infrastruktur[at]tso[dot]de
+49 (541) 1395-94